Bring-your-own serverless
Here I talk about the implications of building your own serverless architecture, why you might do it, and in particular the security concerns that come with that.
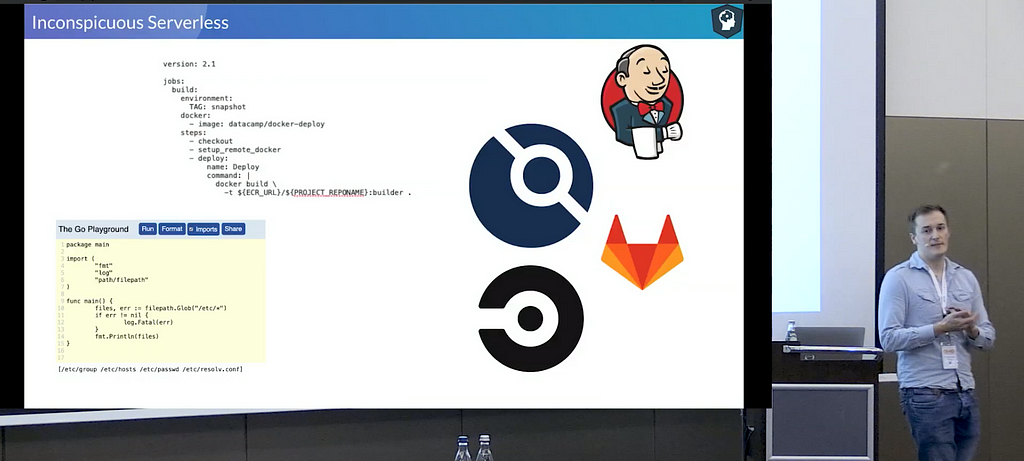
Useful for everyone is where we talk about how you’re already using serverless, i.e. in CI platforms, and why everyone should be aware of the implications of what they’re doing. Only recently I saw an exploit based on custom code being injectable into a CI process that was never considered in the flow of code hence permissions left wide open.
Hopefully, this will give you some new insight into why serverless isn’t just built on magic, and how to both use and secure it for your purposes.
Michael Pollett
Bio LinkedIn DNS CAA Tester
docker, development, continuous-integration, security, serverless
